A checksum is a sequence of numbers and letters used to check data for errors. If you know the checksum of an original file, you can use a checksum utility to confirm your copy is identical.
To produce a checksum, you run a program that puts that file through an algorithm. Typical algorithms used for this include MD5, SHA-1, SHA-256, and SHA-512.
The algorithm uses a cryptographic hash function that takes an input and produces a string (a sequence of numbers and letters) of a fixed length. The input file can be a small 1 MB file or a massive 4 GB file, but either way, you’ll end up with a checksum of the same length. Checksums may also be called “hashes.”
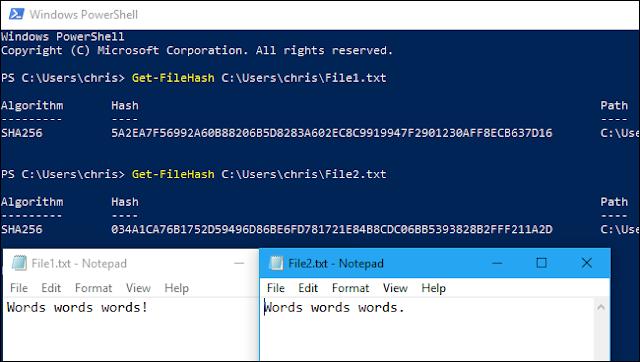
Small changes in the file produce very different looking checksums. For example, we created two different text files that are almost the same, but one has an exclamation point where the other has a period. After running Windows 10’s built-in checksumming utility on them, we saw very different checksums. A single character difference in the underlying file produces a very different looking checksum.
You can use checksums to check files and other data for errors that occur during transmission or storage. For example, a file might not have properly downloaded due to network issues, or hard drive problems could have caused corruption in a file on disk.
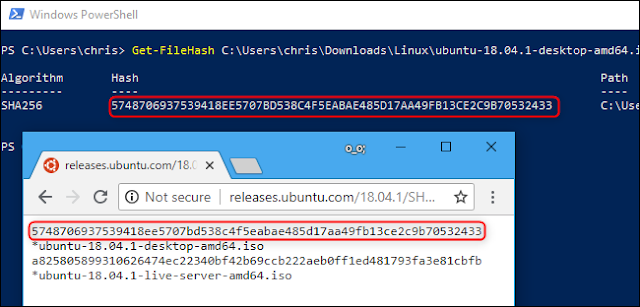
If you know the checksum of the original file, you can run a checksum or hashing utility on it. If the resulting checksum matches, you know the file you have is identical.
Computers use checksum-style techniques to check data for problems in the background, but you can also do this yourself. For example, Linux distributions often provide checksums so you can verify your Linux ISO properly downloaded before burning it to a disc or putting it on a USB drive. You could also use checksums to verify the integrity of any other type of file, from applications to documents and media. You just need to know the checksum of the original file.
What’s the Difference Between MD5, SHA-1, and SHA-256 Sums?
Checksums are a useful way to ensure that a file doesn’t have an error. If a random error occurs due to download problems or hard drive issues, the resulting checksum will be different, even if it’s just a tiny error.
However, these cryptographic hash functions aren’t perfect. Security researchers have found “collisions” with the MD5 and SHA-1 functions. In other words, they’ve found two different files that produce the same MD5 or SHA-1 hash, but are different.
This is unlikely to happen through random chance, but an attacker could use this technique to disguise a malicious file as a legitimate file. That’s why you shouldn’t rely on MD5 or SHA-1 sums to verify that a file is authentic just to check for corruption.
There haven’t been any reports of an SHA-256 collision yet, which is why applications are now creating SHA-256 sums instead of MD5 sums and SHA-1 sums. SHA-256 is a stronger, more secure algorithm.
Different checksum algorithms produce different results. A file will have different MD5, SHA-1, and SHA–256 checksums. If you only know the MD5 sum of an original file, you must calculate your copy’s MD5 sum to check if it’s a match.
How to Calculate Checksums
If you know the checksum of an original file and want to check it on your PC, you can do so easily. Windows, macOS, and Linux all have built-in utilities for generating checksums. You don’t need any third-party utilities.
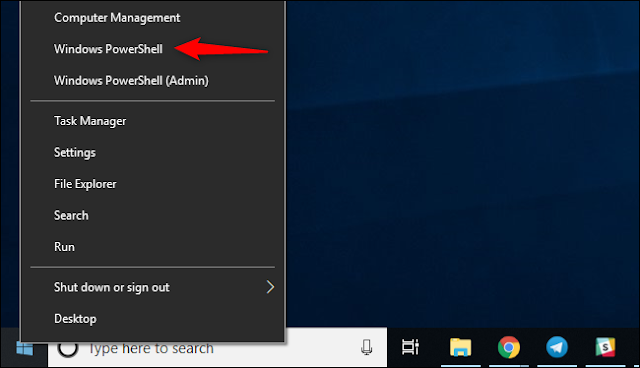
On Windows, PowerShell’s Get-FileHash command calculates the checksum of a file. To use it, first open PowerShell. On Windows 10, right-click the Start button and select “Windows PowerShell.” You can also launch it by searching the Start menu for “PowerShell” and clicking the “Windows PowerShell” shortcut.
Type the path of the file you want to calculate the checksum for. Or, to make things easier, drag and drop the file from a File Explorer window onto the PowerShell window to automatically fill in its path.
If you need another type of checksum, add the appropriate -Algorithm option to the end of the command, like so:
Get-FileHash C:pathtofile.iso -Algorithm MD5
Get-FileHash C:pathtofile.iso -Algorithm SHA1
Compare the calculated checksum to the original one. You shouldn’t have to look too close, as there will be a massive difference in the checksum even if there’s only a tiny difference in the underlying file.